By Señior Tech from the February 2017 Edition
Today I was racking my brain about what I could write about this month and like being hit by a 2 x 4 across my head, I read my email to find …
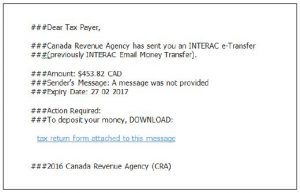 I have disabled the hyperlink above, but if I had clicked it, I would have downloaded the following file.
I have disabled the hyperlink above, but if I had clicked it, I would have downloaded the following file.
http://luvzizfashion.com/Tax Refund ID 16677893623 PDF DOCUMENT.zip
The file is meant to look like a PDF document, but it is, in fact, a zipped file of an executable program. Although I didn’t open the file or go to the site, I am 99.999% certain the program would load onto the computer of the person who did.
There are several scenarios that could occur:
Ransomware the computer is locked and will not function until you call a number and give your credit card information to unlock the code. Of course, if you do the crooks will now have your credit card information.
Identity theft by filling out the fake form, the information you provide, could be used to apply for credit in your name.
Key stroke logger the code could open a back door to your operating system and your passwords and User IDs could be harvested. With these credentials, the crook could hijack your Facebook account, your email or even log in to your online banking account.
Botnet – your computer could then be controlled as part of a network of hijacked computers to shut down sites online.
The Reply-To address was listed as Reply-To: Revenue Agency 2017
But in fact, was from Irene@datanetlink.com.br – this person most likely did not send this email and is probably one of the crook’s victims.
You can find this information by right-clicking your mouse on the reply-to email address in your email client (program you use to read email).
Whenever an unsolicited email message arrives in your inbox offering something you did not expect, be very wary. Banks, Federal Government Agencies or businesses, do not send these types of communications.
Never click on links within unsolicited emails. If you have a question about the validity, contact the sender by telephone (look up the number online rather than trusting the one provided in the email) or go directly to their website that you type in (do not use links that are in the email).
I have talked to a few people who had their computers com-promised and it cost them time, money and inconvenience to restore their systems.
The bait in the email was the $482.53, that is probably what I would have to pay them to get back the control of my computer.
if you have questions or suggestions about future technology topics, email seniortech@manzanillosun.com
Download the full edition or view it online
—
Señior Tech is a technology addict that loves to share tips. He lives in Manzanillo full time and helps keep the community up on the latest tech tricks and toys.